![]()
นักวิจัยด้านความมั่นคงปลอดภัยนาม Xylitol ออกมาแจ้งเตือนถึง Ransomware ตัวใหม่ ชื่อว่า Satan ให้บริการแบบ Ransomware-as-a-Service (RaaS) ช่วยให้อาชญากรไซเบอร์สามารถสร้าง Ransomware เป็นของตัวเอง พร้อมแพร่กระจายเรียกค่าไถ่เหยื่อทั่วโลก
Satan เป็น Ransomware-as-a-Service ที่ช่วยให้ผู้ไม่ประสงค์ดีที่ถึงแม้จะไม่มีความรู้เชิงเทคนิค สามารถสร้างและปรับแต่ง Ransomware เป็นของตัวเองได้ ในขณะที่ RaaS จะเป็นตัวจัดการการชำระเงินค่าไถ่และคอยอัปเดตฟีเจอร์ใหม่ๆ ให้ ค่าไถ่ที่ได้รับแต่ละครั้งจะถูกหักออก 30% เพื่อเป็นค่าบริการของ RaaS แต่ถ้าสามารถหาเหยื่อจ่ายค่าไถ่ได้มากเท่าไหร่ ค่าบริการที่หักออกมานี้ก็จะลดลงมากเท่านั้น
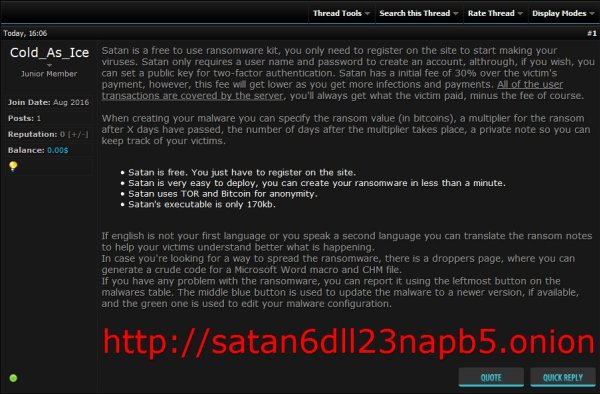
ภาพด้านล่างแสดงหน้า Homepage ของ Satan SaaS ซึ่งจะแนะนำ Ransomware อธิบายถึงบริการ และวิธีที่ผู้ไม่ประสงค์จะใช้ Satan เพื่อทำเงิน
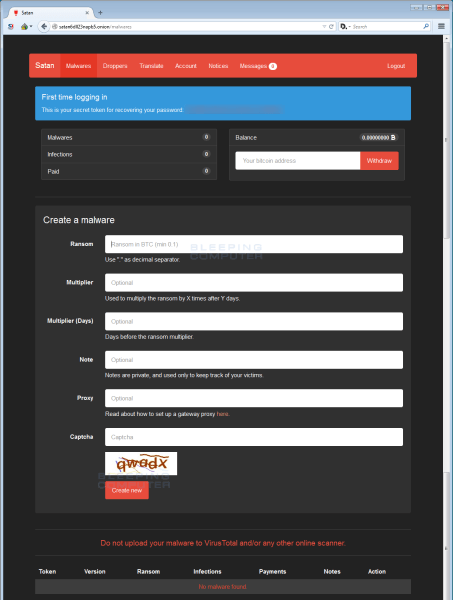
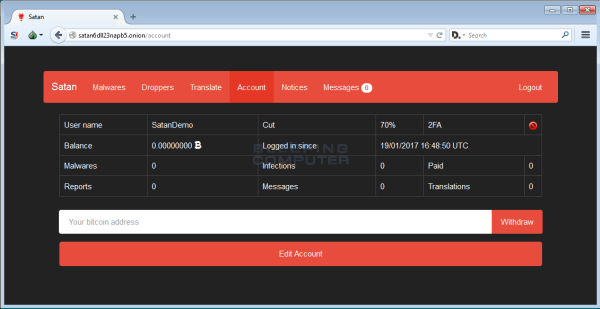
เมื่อผู้ไม่ประสงค์ดีลงทะเบียนและล็อกอินเข้าสู่หน้าหลัก พวกเขาจะเจอหน้า Console ซึ่งประกอบด้วย Page จำนวนมากสำหรับช่วยสร้าง ปรับแต่ง และแพร่กระจาย Ransomware ไม่ว่าจะเป็น Malwares, Droppers, Translate, Account, Notices และ Messages
หน้า Malwares ด้านล่าง เป็นหน้าแรกหลังจากที่ล็อกอินเข้ามา สำหรับให้ผู้ไม่ประสงค์ดีตั้งค่าต่างๆ ของ Ransomware ให้เป็นเวอร์ชันสำหรับตัวเอง โดยสามารถระบุจำนวนเงินที่จะเรียกค่าไถ่ ระยะเวลาที่จะให้เริ่มทำงานหลังติดต่อ และจำนวนวันที่เหยื่อต้องจ่ายค่าไถ่ก่อนที่ค่าไถ่จะเพิ่มจำนวนขึ้น เป็นต้น
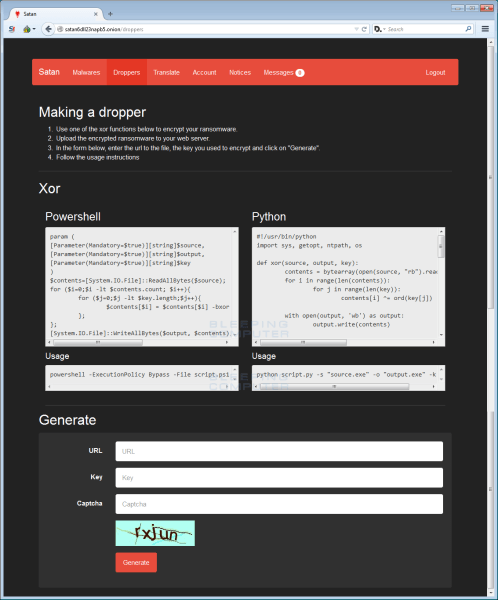
หน้า Droppers เป็นโค้ดที่ช่วยให้ผู้ไม่ประสงค์ดีในการสร้าง Microsoft Word Macros หรือ CHM Installers แปลกปลอม เพื่อใช้ในการแพร่กระจายมัลแวร์ผ่านทาง SPAM หรือช่องทางอื่นๆ ได้
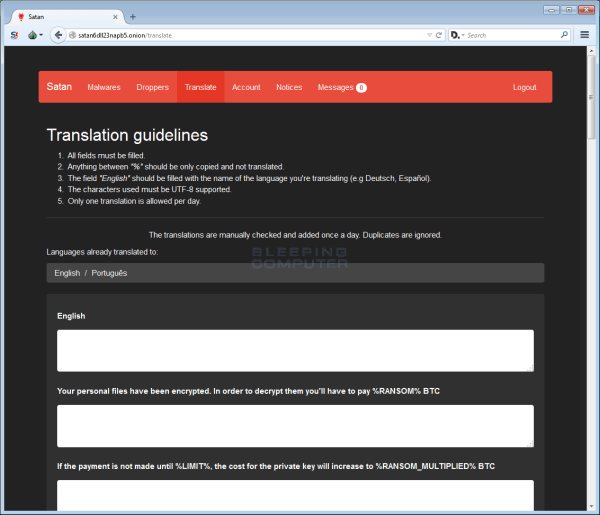
หน้า Translate ช่วยให้ผู้ไม่ประสงค์ดีสามารถแปลและเพิ่มภาษาท้องถิ่นของตนหรือภาษาอื่นๆ บนข้อความเรียกค่าไถ่ของ Satan ได้
หน้า Account ด้านล่างถูกใช้เพื่อแสดงจำนวนคนที่ติดมัลแวร์ Satan ที่ได้แพร่กระจายออกไป จำนวนเงินค่าไถ่ที่ได้รับ และข้อมูลอื่นๆ
สุดท้ายคือหน้า Notices สำหรับรับข้อมูลข่าวสารจากแฮ้คเกอร์ผู้พัฒนา Satan Raas และหน้า Messages สำหรับร้องขอ “Customer Service”
หลังจากที่แพร่กระจาย Satan Ransowmare ไปแล้ว เมื่อเหยื่อเผลอดาวน์โหลดและเปิดไฟล์ที่มี Ransomware ฝังอยู่ Satan จะตรวจสอบก่อนว่าตัวมันเองรันอยู่บน Virtual Machine หรือไม่ ถ้ารันอยู่ ก็จะปิดการทำงานของตัวเอง เพื่อหลบเลี่ยงระบบป้องกันภัยคุกคามแบบ Sandboxing แต่ถ้ารันอยู่บนคอมพิวเตอร์ มันจะแทรกตัวเองเข้าไปใน TaskHost.exe และเริ่มเข้ารหัสข้อมูลทั้งหมดบนคอมพิวเตอร์ ไม่ว่าจะเป็นไฟล์ข้อมูลเอกสาร วิดีโอ รูปภาพ เพลง และอื่นๆ ซึ่งขณะนี้ยังไม่ทราบแน่กชัดว่าอัลกอริธึมที่ใช้เข้ารหัสข้อมูลคืออะไร
จากนั้น Satan จะเปลี่ยนชื่อและต่อท้ายนามสกุลไฟล์ด้วย .stn เช่น test.jpg ไปเป็น ahasd.stn และสร้างข้อความเรียกค่าไถ่ภายใต้ไฟล์ที่ชื่อ HELP_DECRYPT_FILES.html ในแต่ละโฟลเดอร์ที่มีไฟล์ถูกเข้ารหัส หลังจากที่เข้ารหัสข้อมูลทั้งเครื่องเสร็จเรียบร้อย Satan จะรันคำสั่ง C:\Windows\System32\cipher.exe” /W:C เพื่อล้างข้อมูลทั้งหมดบนพื้นที่ที่ไม่ได้ใช้ของไดรฟ์ C
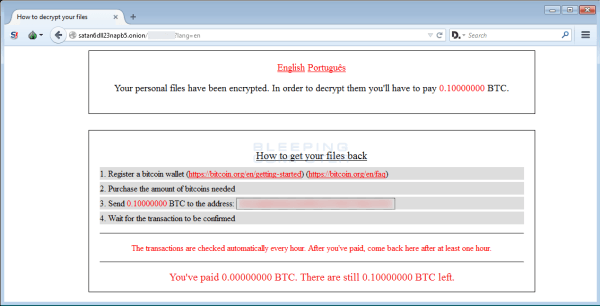
ข้อความเรียกค่าไถ่แสดงดังรูปด้านล่าง ซึ่งระบุ Victim ID และ URL สำหรับเชื่อมโยงไปยังเครือข่าย Tor เพื่อชำระค่าไถ่
จนถึงตอนนี้ ยังไม่มี Decrypter สำหรับปลดรหัส Ransomware ดังกล่าว
ที่มา : techtalkthai
ลิงค์ : https://www.techtalkthai.com/satan-ransomware-review/